Windows NPS Radius Authentication of Cisco Prime Infrastructure
As part of a recent network upgrade I was able to get Cisco Prime Infrastructure included in the moneys for the project. I love new systems to play with, of course, and immediately got to work checking out all the bells and whistles. Needless to say, it wasn’t long until I got tired of remembering the root credentials and began looking at RADIUS authentication for some help. Additionally, I’m kind of the security guy too and knew I was breaking my own rules by not having individual user logons in place.
At any rate, I fired up the management console for NPS on the respective windows ’08 box and chopped out a policy. I added my “Net Admins” group from Active Directory and specified the NAS IP address for Prime. Jumping over to Prime I threw my credentials in only to receive an “Invalid Username or Password” message.
I tried again, same thing. I knew my credentials were right so back to the NPS server I went. Sure enough, the logs were actually showing Access Accept messages were being sent back to Prime.
Let me stop for a second and say that before this endeavor I knew only the basics of Radius as it pertains to Cisco but have since gained a significant chunk of knowledge with a lot of guessing and checking to validate it all.
Cisco Prime, like anything IOS, understands most options through Attribute Value Pairs aka “AV-Pairs”. This is actually true for both Radius and TACACS! There are some pairs that are exclusive to TACACS (such as cmd=x and cmd-arg=x) but the majority, including the one I will be discussing here, work without trouble.
So how does one get the needed AV-Pair information for Prime? Simple, navigate to Administration -> Users, Roles and AAA -> User Groups. Next, click the “Export” button to the right of the group name that has permissions you would like to bestow upon you Radius authenticated user.
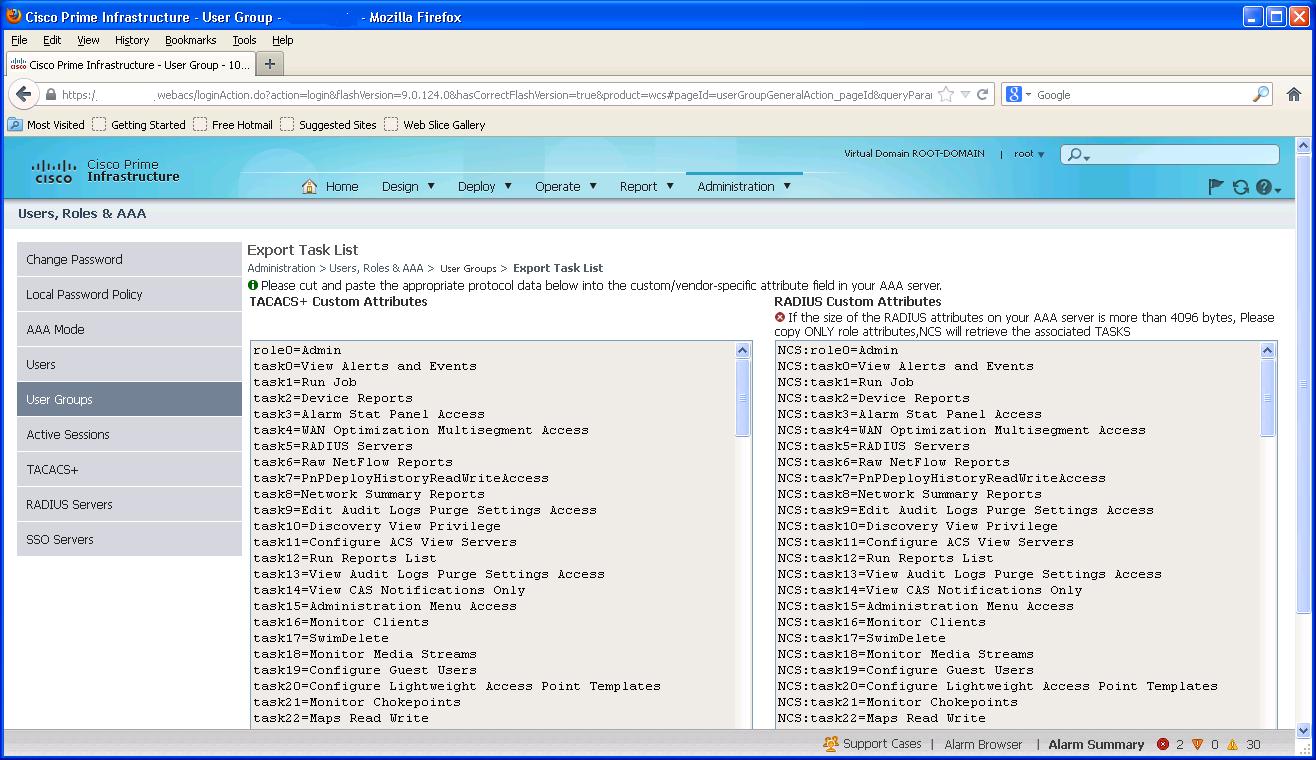
Since this article is focused on getting this all to work with the Windows NPS implementation of Radius I want to share another point. Windows cannot send more than 4096 bytes of data in its Radius responses. I know this because I copied all 100 some AV pairs into the configuration only for it to NOT work. That really irritated me to say the least. However, if you’re using a TACACS system of some type you will have to send all AV-Pairs.
At any rate the “role” pair is all that’s needed as the on screen message alludes to.
I added this information to my policy and it STILL didn’t work. I’ll be honest; by this point I had a TAC case wide open with Cisco and the emails where flowing but the actual answer to the problem wasn’t. Finally, as if it was common knowledge from the first few pages of the manually, the technician asks if I had specified the Virtual Domain AV-Pair. Of course, the answer was no.
The million dollar string was something like this:
NCS:virtual-domain0=ROOT-DOMAIN
I added this to the NPS config and finally; it worked!
To circle back around the NPS setup uses the Vendor Specific AV-Pair option as you can see in the screen shot below.

I won’t go into the other details of the configuration here but if you have questions feel free to let me know.
I also wanted to include some documents that pertain to this quest that I found helpful:
1. http://www.cisco.com/en/US/docs/ios/sec_user_services/configuration/guide/sec_rad_ov_ietf_attr.html
2. http://www.cisco.com/en/US/docs/ios/12_2/security/configuration/guide/scftacat.pdf
3. http://www.cisco.com/en/US/docs/wireless/prime_infrastructure/1.3/configuration/guide/pi_13_cg.pdf
Thanks! This also works for 2003 IAS. Edit Profile > Advanced > Add > Cisco-AV-Pair ….
Typo in NCS:virtual-domain0=ROOT-DOAMIN should be DOMAIN. 😉
Thanks! Updated the Typo as well
We had issues with Radius on our Cisco Prime installation that we couldn’t resolve.
We tried every configuration we could think of . . .
Eventually, we called Cisco support. They walked us through doing the same things that we had already done.
The last thing the support technician told us was to try re-installing the ova (this was a virtual implementation).
We re-downloaded the OVA file and re-installed Cisco Prime. To our surprise, it immediately started working.
We were even able to import the configuration setting from the original installation.
I hope that helps.
Hi
Great post, and it seems I’m 98% of the way to making it work, but I still get the “Invalid Username and/or password.
Would you mind sharing all of your NPS policy properties? I have mine set up with CHAP authentication, Framed Protocol PPP, Service-type Framed and the Cisco-AV-Pairs you detailed. The radius log reads like this:
02/17/2015 07:18:08.540
MyServer
IAS
MyPrimeIP
1
5
MyDomain\MyUserName
MyPrimeIP
0
05PrimeInfrastructure
UseWindowsauthentication for all users
1
MyDomain\MyUserName
MyDomain\MyUserName
311 1 MyRADIUSIP 01/17/2015 15:18:35 3437870
2
1
0
This is an IAS_SUCCESS authentication package, so authentication seems to be granted, but I can’t figure out the “Class” information that is sent back, and I can’t find the Cisco AV Pairs anywhere. Also, should I be worried that the timestamp and the Class data has a time difference of some 8 hours?
Unfortunately I do not currently have an instance of Prime running in my lab. The AV Pairs have to be manually created in your policy the same way they are shown in the last screenshot in this article.
You many need to get in and see the debug logs in PI its self.