Authenticating APC Network Management Cards with Network Policy Server
Working in a large environment with 100% power availability as a requirement I have had the experience of working with many APC UPS systems. We typically monitor the UPS remotely and from time to time have to log in to check statuses or review errors. Our environment frowns upon shared credentials as do I so authentication to these systems had to be updated. I knew we had options because I had seen RADIUS authentication listed in the specifications for the management card.
Initially I created a fairly vanilla policy and was able to log into the APC’s. The issue, however, was that the access level I received was a read only level. To fully administer the unit there was something else that had to be returned to the unit via radius. After some serious searching and experimentation through the documentation I found the answer.
First, be sure your APC unit is defined as a client in NPS. Next, create a network policy to process the authentication request. My policy was configured as follows:
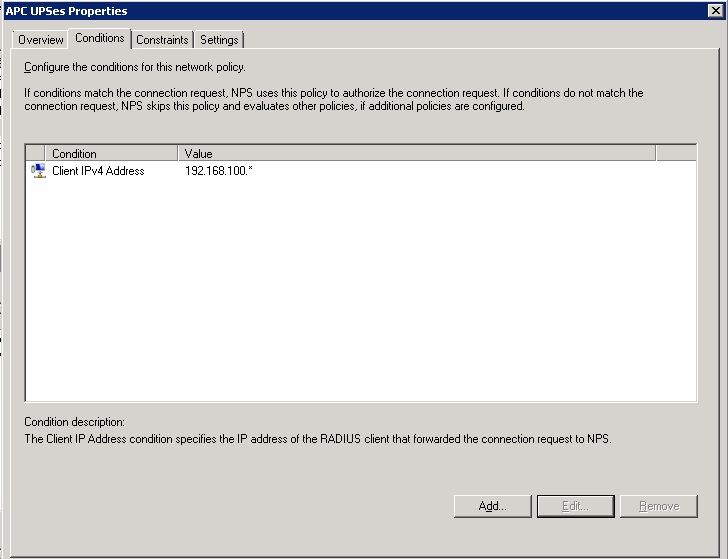
- First, I filter I would add some items under the conditions tab. For me setup I limited the IP addresses that connections could come from with the “Client IPv4 Address” option. You will also have to add a “Windows Group” to control the users who have access.
- Under the “Constraints” tab I selected “PAP” authentication since that is all the APC supports.

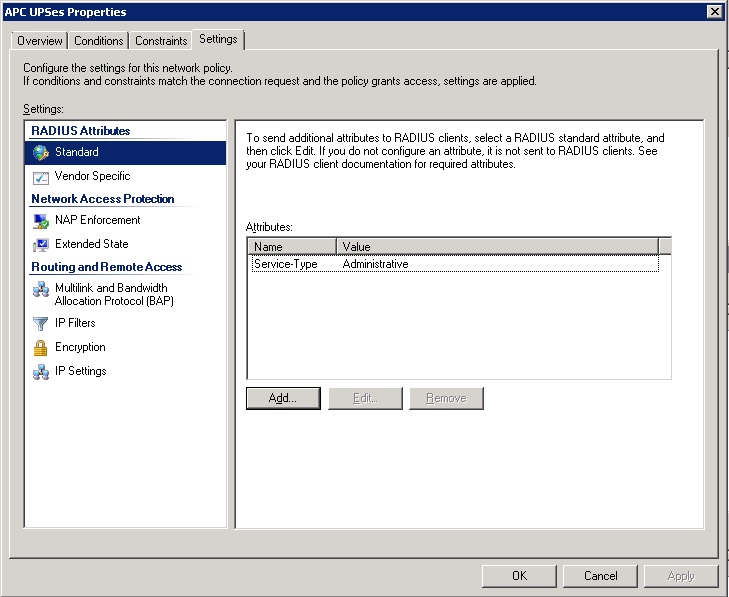
- Under the “Settings” tab we can configure the settings that get sent back to the Radius client. In this case, the APC UPS. We will want to use the “Service-Type” attribute and will want to set its values to “Administrative” to allow full administrator access or to “login” to allow only limited read only access.
Assuming your Radius Client is added correctly to NPS, and the client its self is pointing to the Radius server you should now be able to authenticate.
One downfall to this setup is that you cannot log in as the “apc” username while Radius is configured. Be aware of this! The best option I have for getting back into the APC unit with the local username while Radius is enabled is to disable the UPS’s corresponding Radius client in the NPS server configuration.
I Hope this was helpful to someone!
Depending on the age of your management card (I have an AP9617, flashed to the latest firmware), you can specify “RADIUS Only” under Administration > Security > Remote users > Authentication > Authentication Method.
I would still prefer to have local authentication as a backup in the event I lose my links to the RADIUS server, whether the event is due to a fibre cut or some kind of trenching incident that knocked out a remote site.
If you want to provide true read-only access, the service-type should be set to Authorize only, which doesn’t allow for any changes at all. With the service-type set to Login, the user still can reboot the ups.
John,
Have you found a way to get local authentication to work while the radius server can be reached? “apc” shows up in the NPS logs as a failed attempt if you try to use its local account password while radius is working…
Thanks, this was helpful. When I originally got the UPS I assumed that the RADIUS options worked like any other and would allow me to login using both local and RADIUS credentials. At this point I got locked out and called APC, who referred me to KB articles that no longer seem to exist. Your article answered the question of how to regain access, so thank you.
Unfortunately, soon after regaining access, I turned the RADIUS option back to ‘Local only’, and now I can’t login again, using RADIUS or the default apc username/password combination. I think I inadvertently left the RADIUS servers configured. Between logging in successfully in RADIUS, and not being able to log in any more, nothing was changed in NPS.
Any suggestions? Can I perform a reset on the management card? If so, how?
I know that really bugs me how those cards are one or the other for authentication.
I just looked at the management card in the UPS I have here. There is a tinny reset pin hole you can use to reset the unit. I have never done it so I am not sure if the entire unit will power cycle just be aware…
Schaeffer, thanks for your reply.
I can confirm it doesn’t reboot the whole unit as I know the management cards run independently of the UPS system.
However, unfortunately all the reset button does is reboot the management card. I’m sure there must be a ‘reset to factory defaults’ option somewhere.
There seems to be a distinct lack of good documentation and also good management and monitoring tools for these mid-range UPSs (we have 2x 20kva SmartUPS). It’s frustrating when other cheaper, simpler devices can do it better.
First, thanks for getting me as far as you have, I really appreciate it. The documentation for this from APC is just appalling.
I’m able to use your settings and some I’ve found elsewhere, and defintely can login with RADIUS. However, I get logged in as “Device Manager” vs “Administrator”. Your instructions match others I’ve seen in relation to the Service-Type=Administrative. Some say to set a Vendor Service type to 318, and set it as Decimal=1 to be Admin, but no combination I’ve found works.
I’m using a “Network Management Card AOS v5.1.7” that came in our new SURT6000XLT, but am having no luck getting that elusive Admin login. Any suggestions?
Thanks!
The only other thing I can really suggest it to check out page 37ish of this document: http://www.apcmedia.com/salestools/ASTE-6Z5QF2_R2_EN.pdf
See if any of it is applicable to your setup. The documentation is certainly lacking I would agree.
You can Disable the RADIUS Client in NPS to restore local login to your UPS
Thanks for the input! Serves as a good reminder to update this post…
The current firmware also has the option to use “RADIUS, then Local Authentication”, under Configuration > Security > Remote Users > Authentication.
Hi,
Great job Technologyordie Team, I’ve been looking for this for some time.
I’m having a problem where the guest/s don’t get time to shut down gracefully before the host powers down. This is testing the command only, I have taken the ups out of the equation for now.
Thanks.
The Service-Type is placed in the wrong policy. You must add a connection policy that replies with the Administrative Service-type in order to gain full access to administrate the device. Go to Connection Request Policies – “Windows Authentication” (is my policy name), Open, Go to settings, Under Radius Attributes go to Standard, Add, Service-type, Value Administrative. You also need to be sure the Radius server is a member of the RAS and IAS Server group and register the server in Active directory. Registering the server in AD does not always add the server to the RAS/IAS server group. Once you do this you will be able to login and have full access to make changes.
@David Chadwick
Thank you, that fixed my problem! Why does no offical documentation mention this!??!
I spent hours trying to figure this out 🙁